NetSecure
Guard Your Net
Product Description
Internet brings us convenience, information and entertainment, but on the other hand, also leaves us vulnerable to information exposure. With the continued presence of Internet worms, viruses, malware and other threats, how we can make use of the network resources without compromising the security becomes a big challenge.
Most of the existing solutions are focused on facing the challenge of network prevention and/or protection against outside attacks such as virus, worms, Trojan and so on, and take countermeasures accordingly, through a firewall, IDS antivirus, antispam, IDP, or UTM system, to control and block the internet in/out traffic that poses a threat to the security. Nevertheless, an intranet threat could cause even more damages than the Internet.
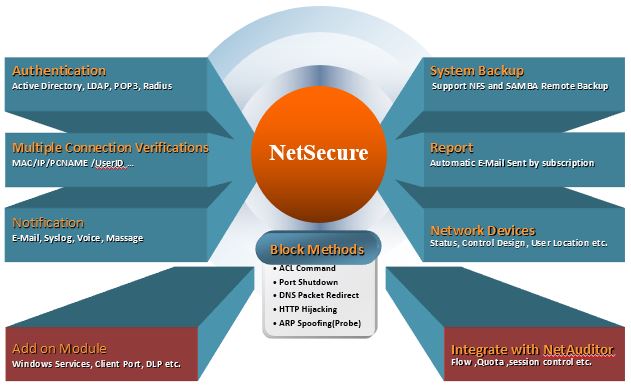
Eye on the intranet issues, EQIT has developed NetSecure to help manage the Intranet access via IP-MAC based control, user authentication or other methods. Without a redesign of the company's existing infrastructure, NetSecure provides a full control over your IP/MAC access points in your network and enforces centrally defined policies in real-time with the ability to block or quarantine suspicious or rogue devices from communicating through the network by various effective blocking technologies. Audit logs, access/incident reports are avaiable to serve the purposes of monitoring and auditing.
Key Features
- Identity Management - A flexible authentication mechanism combined with AD, LDAP, POP3, or RADIUS to ensure granting the right level of network access to people and devices.
- WhiteList Auto-Learning - This feature enables the admin to obtain or learn WhiteList from various sources in different environments.
- Flexible Deployment and Management - The solution is deployed out-of-brand and according to your networking needs without requiring big change to the existing network configuration. The MAC-based enforcement management is strengthened by using a verification of IP or Host Name or User ID to comprise multi-verification combinations.
- Advanced Verification Rule (Extended Module) -Additional verification processes, such as Windows Services, Client Port, Windows Update, Symantec DLP, TrendMicro OfficeScan, Host Name verification or Flow Quota, can be adopted to enhance the security.
- A full Intranet access control by leveraging layer 3 switches.
- Guest System - It allows visitors to access the network, but compliant with the company's security policy.
Unique Features